Logto is an Auth0 alternative designed for modern apps and SaaS products. It offers both Cloud and Open-source services to help you quickly launch your identity and management (IAM) system. Enjoy authentication, authorization, and multi-tenant management all in one.
We recommend starting with a free development tenant on Logto Cloud. This allows you to explore all the features easily.
In this article, we will go through the steps to quickly build the WeCom sign-in experience (user authentication) with Capacitor JS and Logto.
Prerequisites
- A running Logto instance. Check out the introduction page to get started.
- Basic knowledge of Capacitor JS.
- A usable WeCom account.
Create an application in Logto
Logto is based on OpenID Connect (OIDC) authentication and OAuth 2.0 authorization. It supports federated identity management across multiple applications, commonly called Single Sign-On (SSO).
To create your Native app application, simply follow these steps:
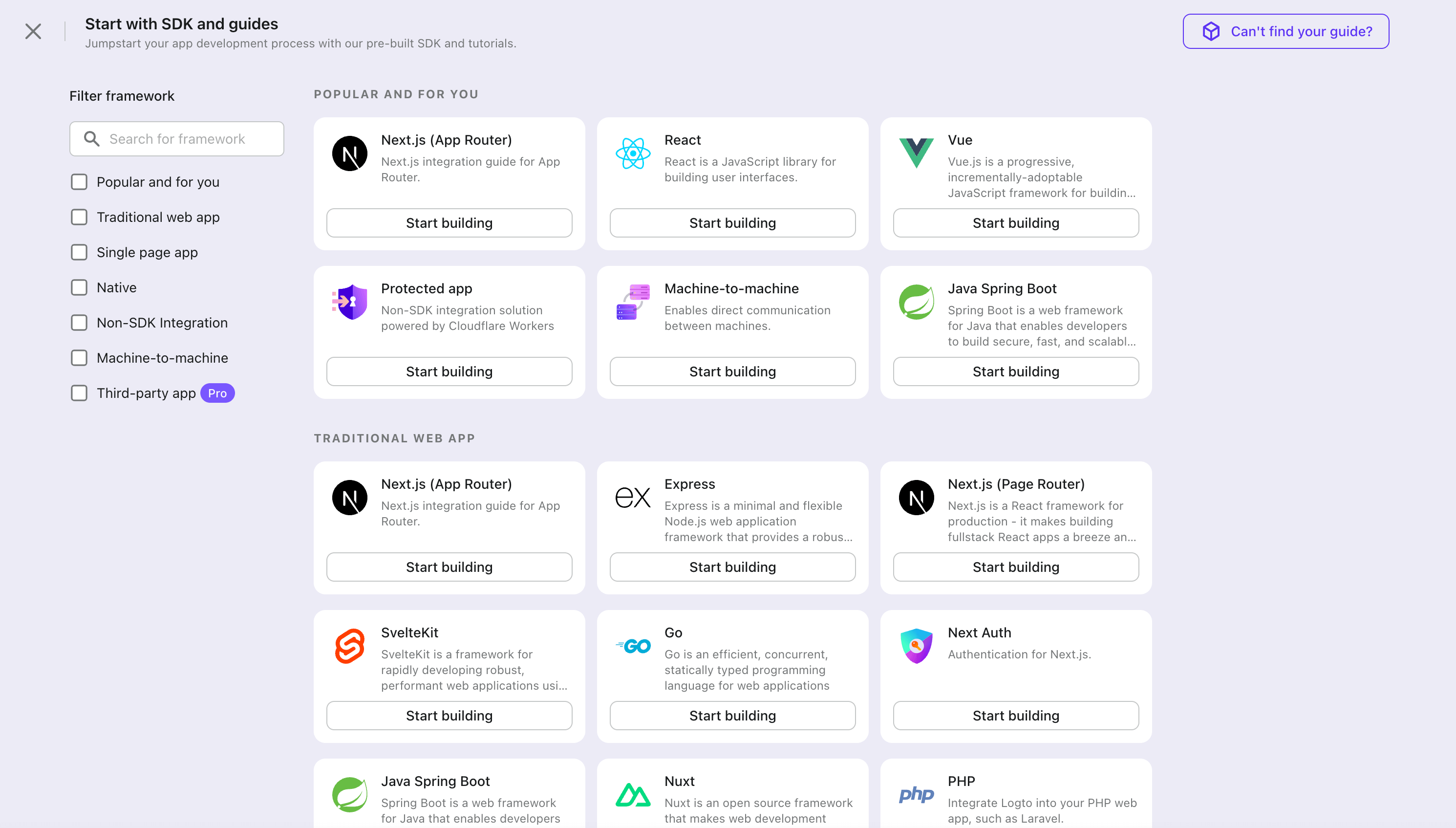
- Open the Logto Console. In the "Get started" section, click the "View all" link to open the application frameworks list. Alternatively, you can navigate to Logto Console > Applications, and click the "Create application" button.
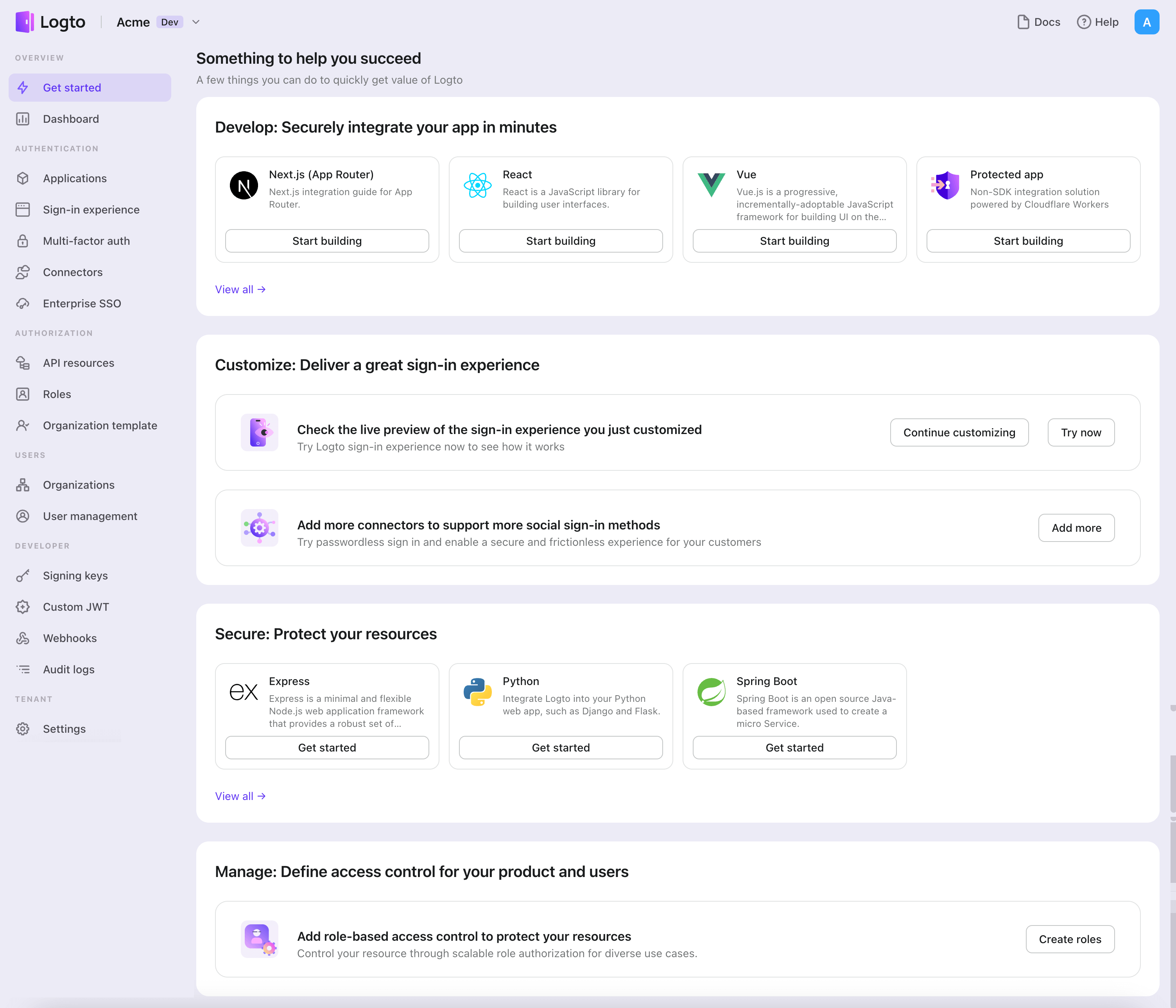
- In the opening modal, click the "Native app" section or filter all the available "Native app" frameworks using the quick filter checkboxes on the left. Click the "Capacitor JS" framework card to start creating your application.
- Enter the application name, e.g., "Bookstore," and click "Create application".
🎉 Ta-da! You just created your first application in Logto. You'll see a congrats page which includes a detailed integration guide. Follow the guide to see what the experience will be in your application.
Integrate Capacitor JS with Logto
- The following demonstration is built on Capacitor JS 5.0.6.
Installation
Install Logto SDK and peer dependencies via your favorite package manager:
- npm
- Yarn
- pnpm
npm i @logto/capacitor
npm i @capacitor/browser @capacitor/app @capacitor/preferences
yarn add @logto/capacitor
yarn add @capacitor/browser @capacitor/app @capacitor/preferences
pnpm add @logto/capacitor
pnpm add @capacitor/browser @capacitor/app @capacitor/preferences
The @logto/capacitor package is the SDK for Logto. The remaining packages are its peer dependencies.
Init Logto client
Add the following code to your Capacitor project:
import LogtoClient, { type LogtoConfig } from '@logto/capacitor';
const logtoConfig: LogtoConfig = {
endpoint: '<your-logto-endpoint>',
appId: '<your-application-id>',
};
const logtoClient = new LogtoClient(config);
Implement sign-in
Before we dive into the details, here's a quick overview of the end-user experience. The sign-in process can be simplified as follows:
- Your app invokes the sign-in method.
- The user is redirected to the Logto sign-in page. For native apps, the system browser is opened.
- The user signs in and is redirected back to your app (configured as the redirect URI).
Regarding redirect-based sign-in
- This authentication process follows the OpenID Connect (OIDC) protocol, and Logto enforces strict security measures to protect user sign-in.
- If you have multiple apps, you can use the same identity provider (Logto). Once the user signs in to one app, Logto will automatically complete the sign-in process when the user accesses another app.
To learn more about the rationale and benefits of redirect-based sign-in, see Logto sign-in experience explained.
Now, let's configure the redirect URI. The redirect URI is used to redirect the user back to your application after the authentication flow.
Ensure that the URI redirects to the Capacitor app, for example, com.example.app://callback. The value may vary depending on your Capacitor app configuration. For more details, see Capacitor Deep Links.
Then, add the following code to the onClick handler of the sign-in button:
const onClick = async () => {
await logtoClient.signIn('com.example.app://callback');
console.log(await logtoClient.isAuthenticated()); // true
console.log(await logtoClient.getIdTokenClaims()); // { sub: '...', ... }
};
Implement sign-out
Since Capacitor leverages the Safari View Controller on iOS and Chrome Custom Tabs on Android, the authentication state can be persisted for a while. However, sometimes the user may want to sign out of the application immediately. In this case, we can use the signOut method to sign out the user:
const onClick = async () => {
await logtoClient.signOut();
console.log(await logtoClient.isAuthenticated()); // false
};
The signOut method has an optional parameter for the post sign-out redirect URI. If it's not provided, the user will be redirected to the Logto sign-out page.
The user needs to click "Done" to close the web view and return to the Capacitor app. If you want to automatically redirect the user back to the Capacitor app, you can provide the post sign-out redirect URI, for instance, com.example.app://callback/sign-out.
Ensure that the post sign-out redirect URI can redirect to the Capacitor app. Then add the following code to the onClick handler of the sign-out button:
const onClick = async () => {
await logtoClient.signOut('com.example.app://callback/sign-out');
};
Checkpoint: Trigger the authentication flow
Run the Capacitor app and click the sign-in button. A browser window will open, redirecting to the Logto sign-in page.
If the user closes the browser window without completing the authentication flow, the Capacitor app will receive a LogtoClientError.
Add WeCom connector
To enable quick sign-in and improve user conversion, connect with Capacitor JS as an identity provider. The Logto social connector helps you establish this connection in minutes by allowing several parameter inputs.
To add a social connector, simply follow these steps:
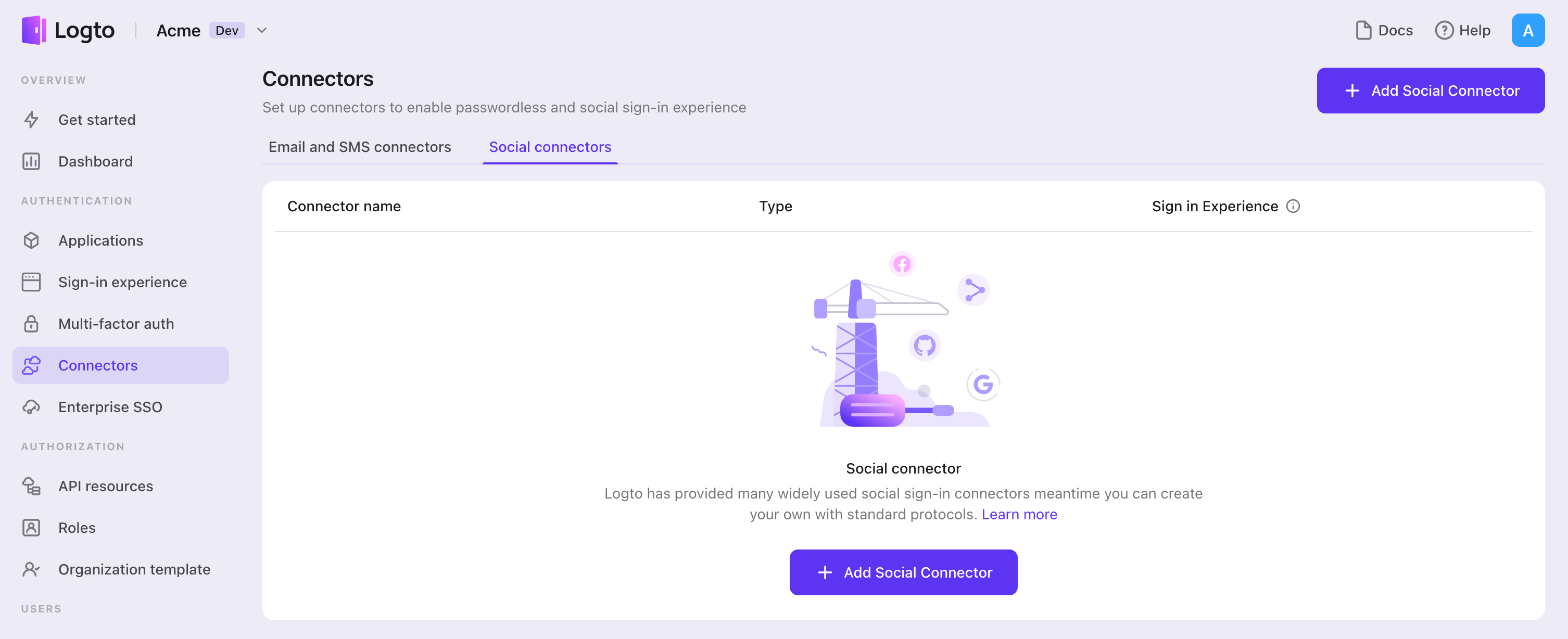
- Navigate to Console > Connectors > Social Connectors.
- Click "Add social connector" and select "WeCom".
- Follow the README guide and complete required fields and customize settings.
If you are following the in-place Connector guide, you can skip the next section.
Set up WeCom app
Get started
Sign in to WeCom WebUI with an admin account or click Manage the enterprise(管理企业) from the WeCom app.
In the "App Management" tab, scroll the page down and click "Create an app".
Fill in the appropriate information according to your app. Then create.
Now we have the Agent ID (NOT APPID) and Secret.
Website info
Set the things you need on this page. It would be like:
- Allowed users: who can see this app
- App Homepage: Your app homepage. E.g.,
logto.io/demo-app
Important There are three items on this page regarding the "Developer API(开发者接口)".
- Web Authorization and JS-SDK;
- Log in to via authorization by WeCom;
- Enterprise Trusted IP;
Fill them according to the guide of WeCom.
Corp ID
If you are familiar with WeChat development, you may notice that the use of Corp ID is the same as APP ID.
You can find the Corp ID at the bottom of the "My Enterprise(我的企业)" tab page. It seems like ww**** .
Configure the connector
So we have the Agent ID, Secret, and Corp ID.
Let's complete the form for the connector.
You can leave the Scope field blank as it is optional. Alternatively, you can fill in snsapi_base or snsapi_privateinfo.
Save and done
Test WeCom connector
That's it. The WeCom connector should be available now. Don't forget to Enable social connector in sign-in experience.
Save your configuration
Double check you have filled out necessary values in the Logto connector configuration area. Click "Save and Done" (or "Save changes") and the WeCom connector should be available now.
Enable WeCom connector in Sign-in Experience
Once you create a social connector successfully, you can enable it as a "Continue with WeCom" button in Sign-in Experience.
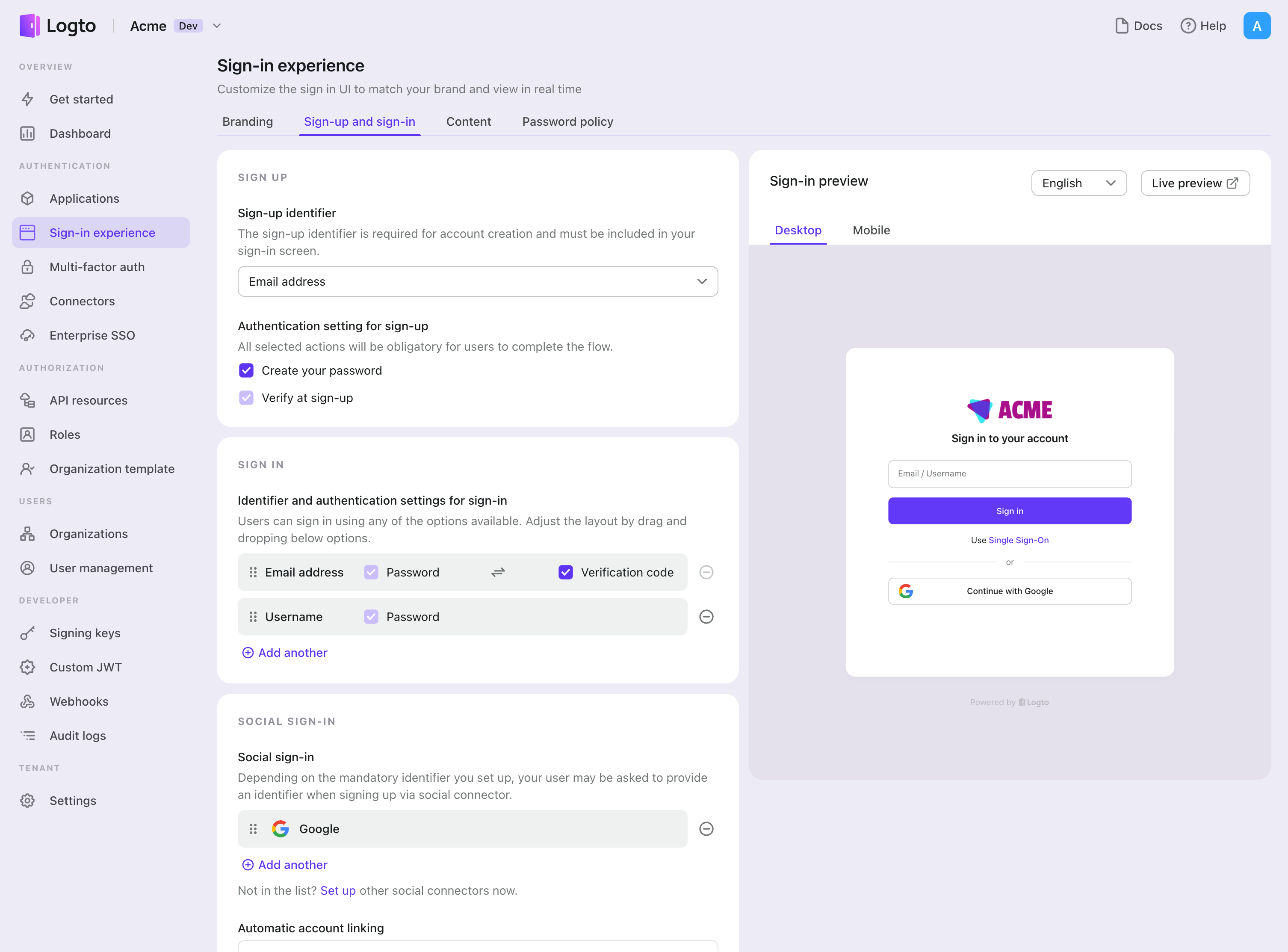
- Navigate to Console > Sign-in experience > Sign-up and sign-in.
- (Optional) Choose "Not applicable" for sign-up identifier if you need social login only.
- Add configured WeCom connector to the "Social sign-in" section.
Testing and Validation
Return to your Capacitor JS app. You should now be able to sign in with WeCom. Enjoy!
Further readings
End-user flows: Logto provides a out-of-the-box authentication flows including MFA and enterprise SSO, along with powerful APIs for flexible implementation of account settings, security verification, and multi-tenant experience.
Authorization: Authorization defines the actions a user can do or resources they can access after being authenticated. Explore how to protect your API for native and single-page applications and implement Role-based Access Control (RBAC).
Organizations: Particularly effective in multi-tenant SaaS and B2B apps, the organization feature enable tenant creation, member management, organization-level RBAC, and just-in-time-provisioning.
Customer IAM series Our serial blog posts about Customer (or Consumer) Identity and Access Management, from 101 to advanced topics and beyond.