Logto is an Auth0 alternative designed for modern apps and SaaS products. It offers both Cloud and Open-source services to help you quickly launch your identity and management (IAM) system. Enjoy authentication, authorization, and multi-tenant management all in one.
We recommend starting with a free development tenant on Logto Cloud. This allows you to explore all the features easily.
In this article, we will go through the steps to quickly build the Aliyun Direct Mail sign-in experience (user authentication) with Webflow and Logto.
Prerequisites
- A running Logto instance. Check out the introduction page to get started.
- Basic knowledge of Webflow.
- A usable Aliyun Direct Mail account.
Create an application in Logto
Logto is based on OpenID Connect (OIDC) authentication and OAuth 2.0 authorization. It supports federated identity management across multiple applications, commonly called Single Sign-On (SSO).
To create your Single page app application, simply follow these steps:
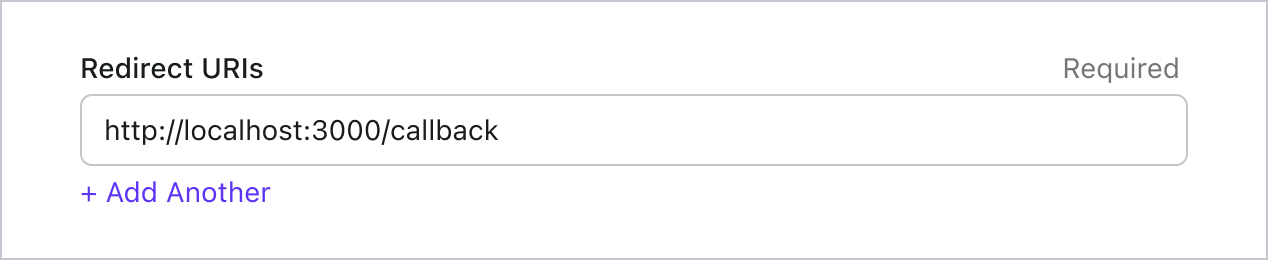
- Open the Logto Console. In the "Get started" section, click the "View all" link to open the application frameworks list. Alternatively, you can navigate to Logto Console > Applications, and click the "Create application" button.
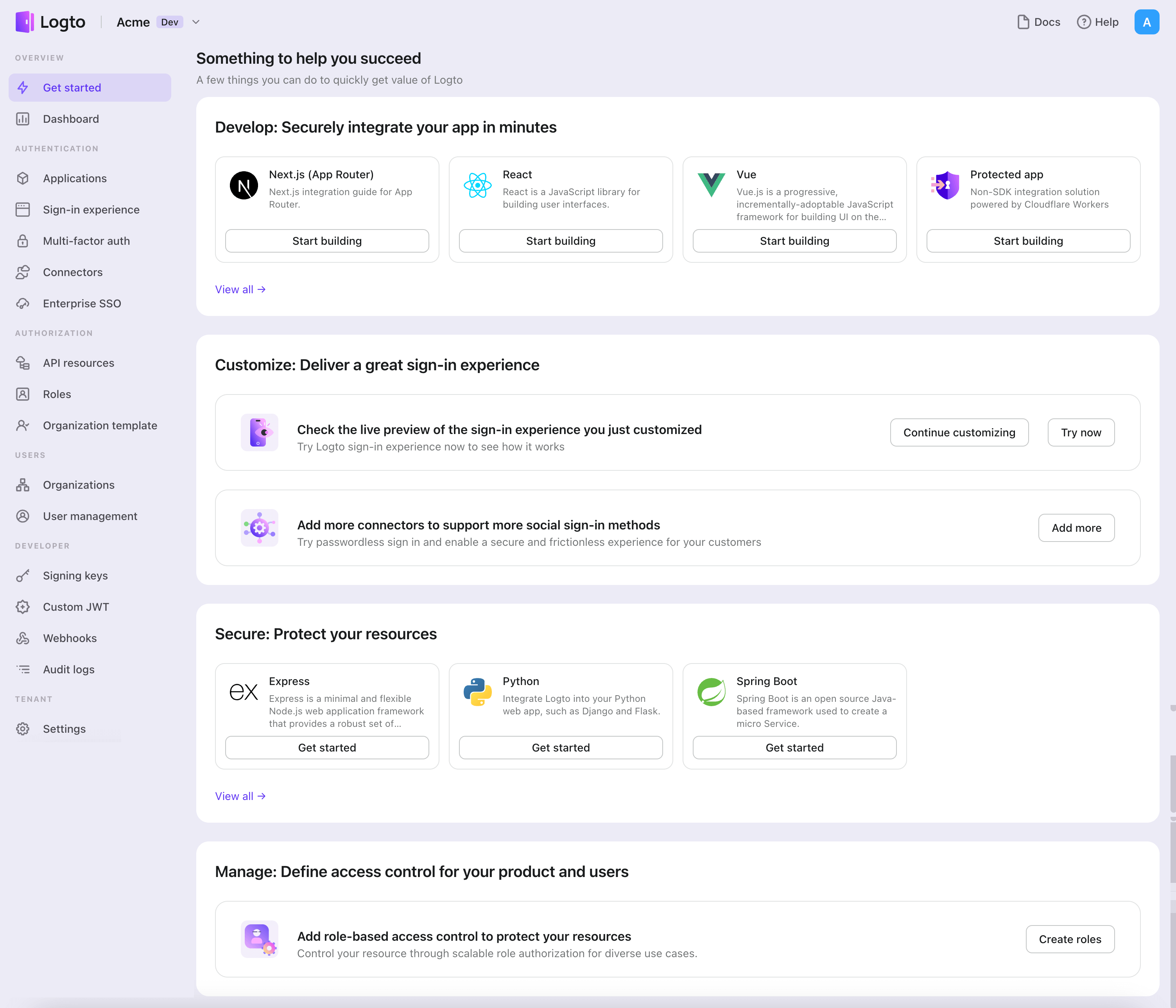
- In the opening modal, click the "Single page app" section or filter all the available "Single page app" frameworks using the quick filter checkboxes on the left. Click the "Webflow" framework card to start creating your application.
- Enter the application name, e.g., "Bookstore," and click "Create application".
🎉 Ta-da! You just created your first application in Logto. You'll see a congrats page which includes a detailed integration guide. Follow the guide to see what the experience will be in your application.
Integrate Webflow with Logto
The sample project is available at Webflow project preview.
Init Logto Provider
In the following steps, we assume your Webflow site is running on https://your-awesome-site.webflow.io.
In this step, we'll add global-level custom code to your Webflow site. Since NPM is not supported in Webflow, we'll use the jsdelivr.com CDN service to import the Logto SDK.
Open the "Site settings" page, and navigate to the "Custom code" section. Add the following code to the "Head code" section.
<script type="module">
// Import \`@logto/browser\` SDK from the jsdelivr CDN
import LogtoClient from 'https://esm.run/@logto/browser';
// Assign the \`logtoClient\` instance to window object,
// enabling global usage in other pages
window.logtoClient = new LogtoClient({
endpoint: '<your-logto-endpoint>', // E.g. http://localhost:3001
appId: '<your-application-id>',
});
</script>
Implement sign-in
Before we dive into the details, here's a quick overview of the end-user experience. The sign-in process can be simplified as follows:
- Your app invokes the sign-in method.
- The user is redirected to the Logto sign-in page. For native apps, the system browser is opened.
- The user signs in and is redirected back to your app (configured as the redirect URI).
Regarding redirect-based sign-in
- This authentication process follows the OpenID Connect (OIDC) protocol, and Logto enforces strict security measures to protect user sign-in.
- If you have multiple apps, you can use the same identity provider (Logto). Once the user signs in to one app, Logto will automatically complete the sign-in process when the user accesses another app.
To learn more about the rationale and benefits of redirect-based sign-in, see Logto sign-in experience explained.
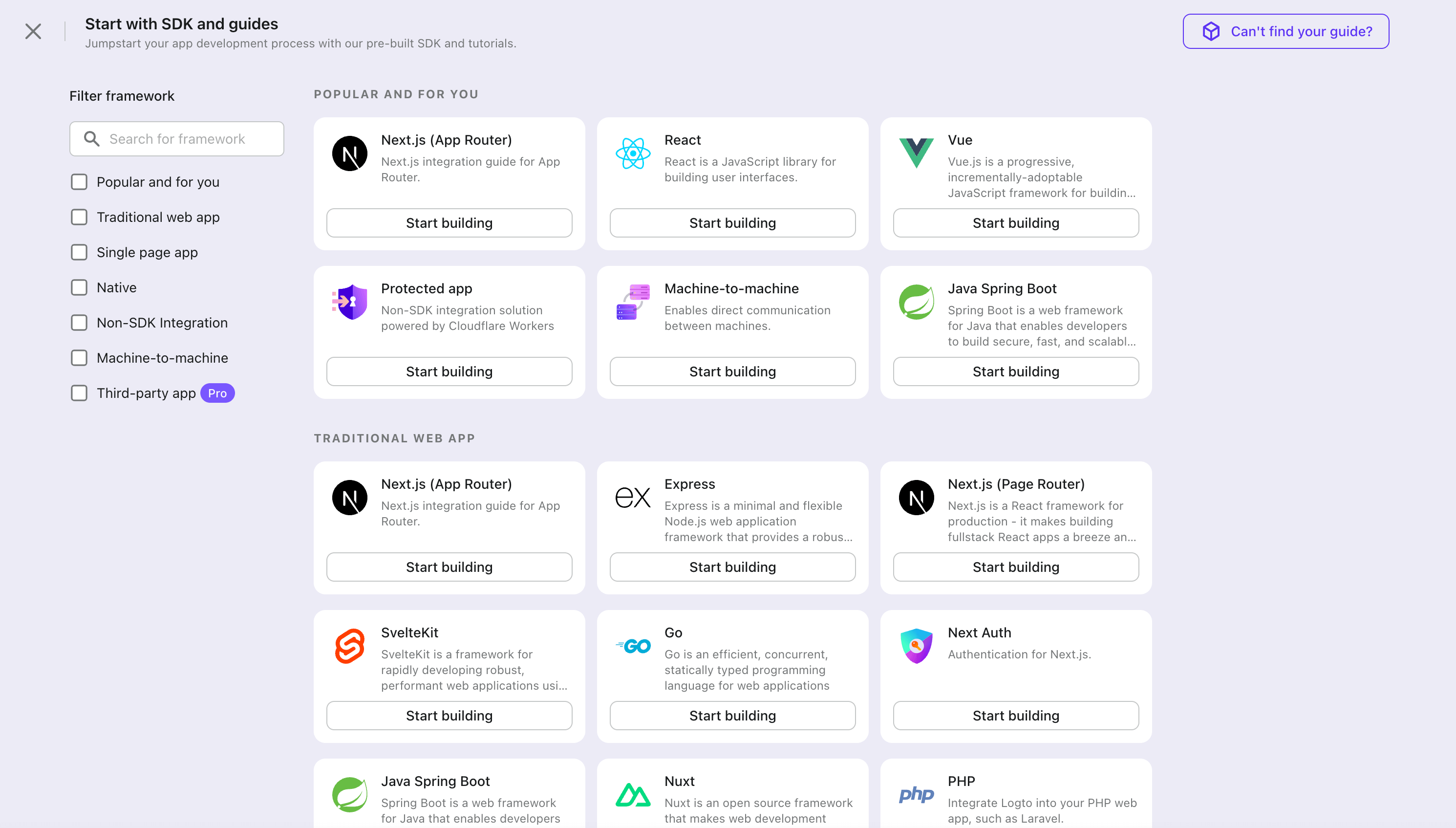
Configure sign-in redirect URI
Let's switch to the Application details page of Logto Console. Add a Redirect URI https://your-awesome-site.webflow.io/callback and click "Save changes".
Implement a sign-in button
Return to your Webflow designer, drag and drop a "Sign in" button to the home page, and assign it an ID “sign-in” for later reference using getElementById().
<script type="module">
const signInButton = document.getElementById('sign-in');
const onClickSignIn = () => logtoClient.signIn('https://your-awesome-site.webflow.io/callback');
signInButton.addEventListener('click', onClickSignIn);
</script>
Handle redirect
We're almost there! In the last step, we use https://your-awesome-site.webflow.io/callback as the Redirect URI, and now we need to handle it properly.
First let's create a "Callback" page in Webflow, and simply put some static text "Redirecting..." on it. Then add the following page-level custom code to "Callback" page.
<script type="module">
(async () => {
// Handle sign-in callback logic by calling the SDK method
await logtoClient.handleSignInCallback(window.location.href);
// Redirect back to the home page when the handling is done
window.location.assign('https://your-awesome-site.webflow.io');
})();
</script>
Implement sign-out
Calling .signOut() will clear all the Logto data in memory and localStorage if they exist.
After signing out, it'll be great to redirect your user back to your website. Let's add https://your-awesome-site.webflow.io as one of the Post Sign-out URIs in Admin Console (shows under Redirect URIs), and use the URL as the parameter when calling .signOut().
Implement a sign-out button
Return to the Webflow designer, and add a “Sign out” button on your home page. Similarly, assign an ID “sign-out” to the button, and add the following code to the page-level custom code.
const signOutButton = document.getElementById('sign-out');
const onClickSignOut = () => logtoClient.signOut('https://your-awesome-site.webflow.io');
signOutButton.addEventListener('click', onClickSignOut);
Handle authentication status
In Logto SDK, generally we can use logtoClient.isAuthenticated() method to check the authentication status, if the user is signed in, the value will be true; otherwise, it will be false.
In your Webflow site, you can also use it to programmatically show and hide the sign-in and sign-out buttons. Apply the following custom code to adjust button CSS accordingly.
const isAuthenticated = await logtoClient.isAuthenticated();
signInButton.style.display = isAuthenticated ? 'none' : 'block';
signOutButton.style.display = isAuthenticated ? 'block' : 'none';
Checkpoint: Test your Webflow site
Now, test your site:
- Deploy and visit your site URL, the sign-in button should be visible.
- Click the sign-in button, the SDK will initiate the sign-in process, redirecting you to the Logto sign-in page.
- After signing in, you will be redirected back to your site, seeing the username and the sign-out button.
- Click the sign-out button to sign-out.
Add Aliyun Direct Mail connector
Email connector is a method used to send one-time passwords (OTPs) for authentication. It enables Email address verification to support passwordless authentication, including Email-based registration, sign-in, two-factor authentication (2FA), and account recovery. You can easily connect Aliyun Direct Mail as your Email provider. With the Logto Email connector, you can set this up in just a few minutes.
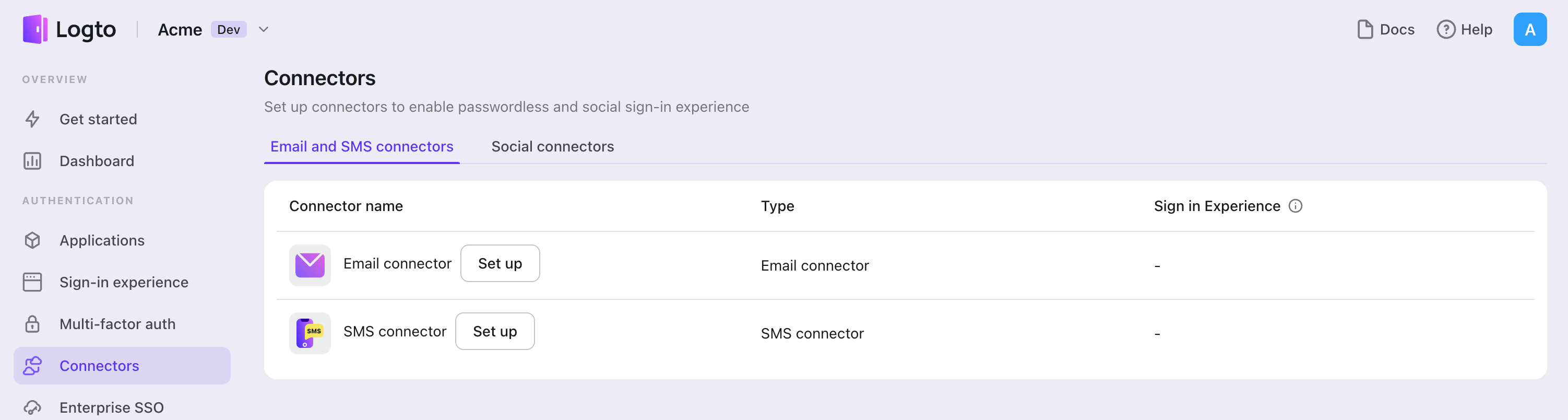
To add a Email connector, simply follow these steps:
- Navigate to Console > Connector > Email and SMS connectors.
- To add a new Email connector, click the "Set up" button and select "Aliyun Direct Mail".
- Review the README documentation for your selected provider.
- Complete the configuration fields in the "Parameter Configuration" section.
- Customize the Email template using the JSON editor.
- Test your configuration by sending a verification code to your Email address.
If you are following the in-place Connector guide, you can skip the next section.
Set up Aliyun email connector
Set up an email service in Aliyun DirectMail Console
Create an Aliyun account
Head to Aliyun and create your Aliyun account if you don't have one.
Enable and configure Aliyun Direct Mail
Go to the DM service console page and sign in. Enable the Direct Mail service by clicking the "Apply to enable" (申请开通) button on the top left of the page and begin the configuration process.
Starting from the DM admin console page, you should:
- Go to "Email Domains" (发信域名) from the sidebar and add "New Domain" (新建域名) following the instructions.
- Customize "Sender Addresses" (发信地址) and "Email Tags" (邮件标签) respectively.
After finishing setup, there are two different ways to test:
- Go to the DirectMail Overview page, find "Operation Guide" (操作引导) at the bottom of the page, and click on "Send Emails" (发送邮件). You will find all the different kinds of testing methods.
- Follow the path "Send Emails" (发送邮件) -> "Email Tasks" (发送邮件) in the sidebar to create a testing task.
Compose the connector JSON
- From the DM admin console page, hover on your avatar in the top right corner and go to "AccessKey Management" (AccessKey 管理), and click "Create AccessKey" (创建 AccessKey). You will get an "AccessKey ID" and "AccessKey Secret" pair after finishing security verification. Please keep them properly.
- Go to the "Sender Addresses" (发信地址) or "Email Tags" (邮件标签) tab you just visited from the DM admin console page, you can find Sender Address or Email Tag easily.
- Fill out the Aliyun DM Connector settings:
- Fill out the
accessKeyIdandaccessKeySecretfields with access key pairs you've got from step 1. - Fill out the
accountNameandfromAliasfield with "Sender Address" and "Email Tag" which were found in step 2. All templates will share this signature name. (You can leavefromAliasblank as it is OPTIONAL.) - You can add multiple DM connector templates for different cases. Here is an example of adding a single template:
- Fill out the
subjectfield, which will work as title of the sending email. - Fill out the
contentfield with arbitrary string-type contents. Do not forget to leave{{code}}placeholder for random verification code. - Fill out
usageTypefield with eitherRegister,SignIn,ForgotPasswordorGenericfor different use cases. (usageTypeis a Logto property to identify the proper use case.) In order to enable full user flows, templates with usageTypeRegister,SignIn,ForgotPasswordandGenericare required.
- Fill out the
- Fill out the
Test Aliyun DM connector
You can type in an email address and click on "Send" to see whether the settings can work before "Save and Done".
That's it. Don't forget to Enable connector in sign-in experience.
Config types
| Name | Type |
|---|---|
| accessKeyId | string |
| accessKeySecret | string |
| accountName | string |
| fromAlias | string (OPTIONAL) |
| templates | Template[] |
| Template Properties | Type | Enum values |
|---|---|---|
| subject | string | N/A |
| content | string | N/A |
| usageType | enum string | 'Register' | 'SignIn' | 'ForgotPassword' | 'Generic' |
Save your configuration
Double check you have filled out necessary values in the Logto connector configuration area. Click "Save and Done" (or "Save changes") and the Aliyun Direct Mail connector should be available now.
Enable Aliyun Direct Mail connector in Sign-in Experience
Once you create a connector successfully, you can enable phone number-based passwordless login and registration.
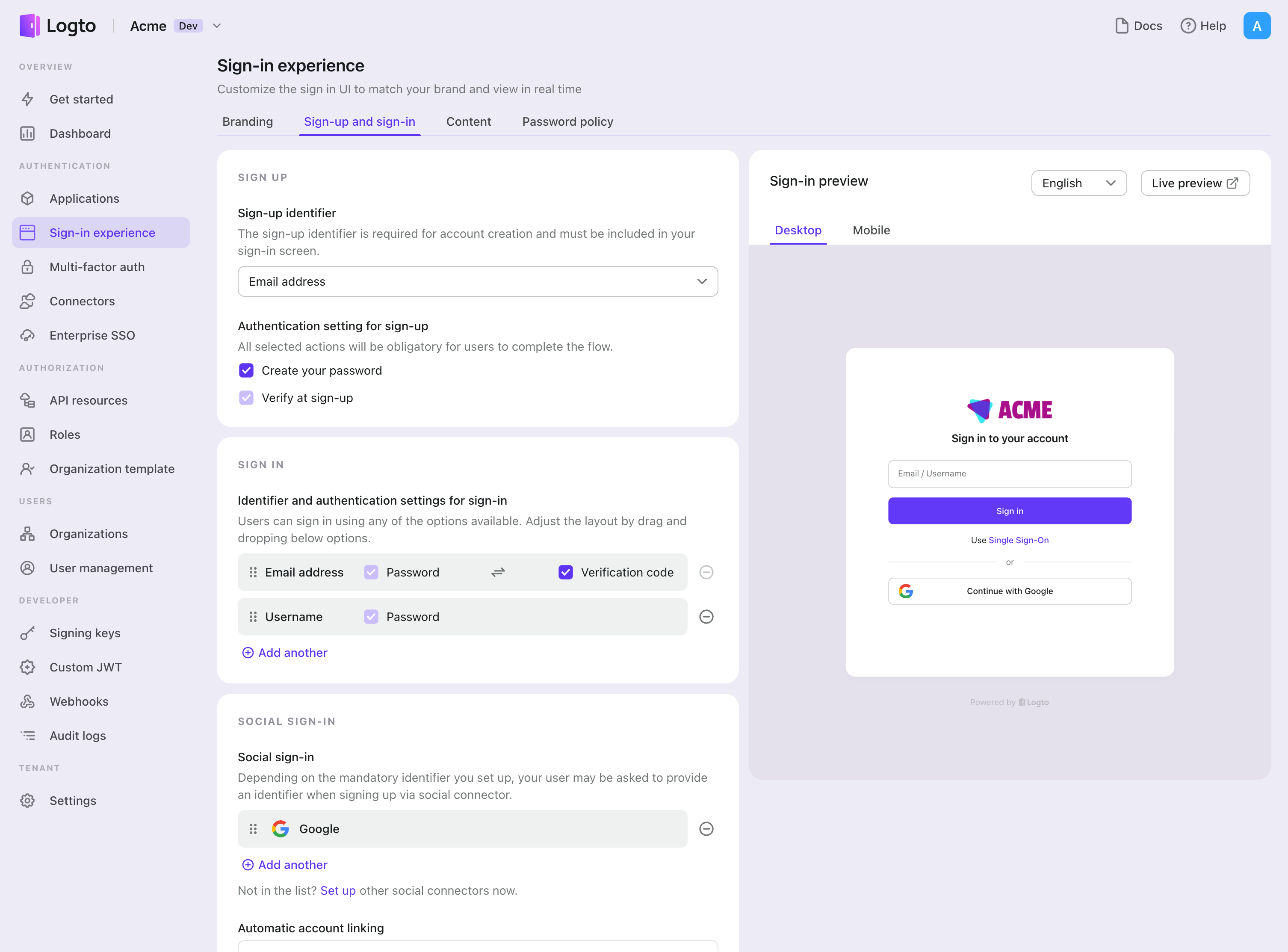
- Navigate to Console > Sign-in experience > Sign-up and sign-in.
- Set up sign-up methods (Optional):
- Select "Email address" or "Email or phone number" as the sign-up identifier.
- "Verify at sign-up" is forced to be enabled. You can also enable "Create a password" on registration.
- Set up sign-in methods:
- Select Email address as one of sign-in identifiers. You can provide multiple available identifiers (email, phone number, and username).
- Select "Verification code" and / or "Password" as the authentication factor.
- Click "Save changes" and test it in "Live preview".
In addition to registration and login via OTPs, you can also have password recovery and -based security verification enabled, as well as linking Email address to profile. See End-user flows for more details.
Testing and Validation
Return to your Webflow app. You should now be able to sign in with Aliyun Direct Mail. Enjoy!
Further readings
End-user flows: Logto provides a out-of-the-box authentication flows including MFA and enterprise SSO, along with powerful APIs for flexible implementation of account settings, security verification, and multi-tenant experience.
Authorization: Authorization defines the actions a user can do or resources they can access after being authenticated. Explore how to protect your API for native and single-page applications and implement Role-based Access Control (RBAC).
Organizations: Particularly effective in multi-tenant SaaS and B2B apps, the organization feature enable tenant creation, member management, organization-level RBAC, and just-in-time-provisioning.
Customer IAM series Our serial blog posts about Customer (or Consumer) Identity and Access Management, from 101 to advanced topics and beyond.